As more and more organizations and employees shift to a work-from-home model, secure external access via Citrix Application Delivery Controllers (ADCs) continue to become even more crucial. As a market leader in the application delivery space, Citrix continues to develop, enhance, secure, and optimize its Citrix ADC hardware and software platforms.
In order to take advantage of some of the latest and greatest enhancements, as well as maintain support agreements, firmware upgrades are necessary. For the most part, new features are released quarterly, while maintenance releases can be expected twice a year. However, organizations are also forced to perform unplanned ADC firmware updates at times to address new and emerging security vulnerabilities. This could mean an organization may perform firmware updates between 5-10 times a year!
While Citrix has done a fantastic job at streamlining the update procedure, proper planning is required to ensure normal operations are not negatively impacted. Unfortunately, this is not always the case, especially if the firmware is applied hastily to address a potentially devastating vulnerability. Things ring even more true as organizations get closer to adopting firmware version 13.1+ if they haven’t already.
So what’s different about version 13.1?
Well, quite a lot, actually. But for the purposes of this article, we will focus primarily on Classic Policy and Function Deprecation. If you are an ADC administrator running firmware version 12.1+, you may have noticed alerts about classic policy deprecation. If not, and you don’t quite believe me, see below:
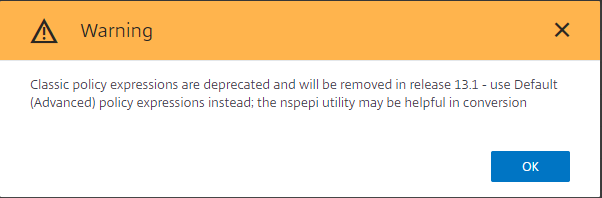
So there it is. Okay, so what now? Simple, switch your policy to advanced! Heck, there is even a tool to assist with this! Well, not so fast. If you are using classic authentication policies, they cannot simply be replaced with advanced authentication policies. Citrix has re-architected its Gateway authentication approach to use the Authentication, Authorization, and Auditing (AAA) component, also known as nFactor. The Citrix nFactor authentication framework uses advanced policies coupled with extensible markup language to provide greater flexibility, control, and customization to present a more intuitive, rich user experience.
This all sounds fantastic right? I can tell you, it is. However, depending on your current setup and desired end state, simply converting from classic policies to advanced will not get your configuration over the finish line. Throw this in with an unplanned, hastily deployed firmware update, and you may end up with an inaccessible access solution.
If this sounds like a position you might find your configuration in, or you’re not quite sure, reach out to Gotham today to help you prepare for, and transition to version 13.1.